If you don't know about the latest trends, how can you act on them?
We are finishing the quarter with the launch of a very exciting solution and some exciting upcoming events, and we want you to be the first to hear about them.
We aim to be our partner's best partner
We are finishing the quarter with the launch of a very exciting solution and some exciting upcoming events, and we want you to be the first to hear about them.

Exertis Security Operations Centre is a 24x7x365 SOC service that provides comprehensive, round-the-clock protection for digital assets. Designed to keep organisations secure from evolving cyber threats, Exertis Security Operations Centre combines advanced technologies, defined processes, and expert human intervention to deliver continuous monitoring and real-time threat detection. Whether you need to enhance your existing resources or opt for a fully managed service, Exertis Security Operations Centre ensures that your sensitive data remains safe and resilient against any potential threats.
What's more: Upcoming events

EmpowHer
We are excited to announce that we are hosting a second EmpowHer event at Lumiere in London on Thursday, October 10th.
This is an incredible opportunity to hear from visionaries in the industry about how we can all work together to make the workplace more inclusive for women. Hear from headline male and female speakers and network and amongst peers from across the industry.
Register an interest
CloudConnect
Following the success of our first CloudConnect Live in-person event in July, the Exertis Cloud team will be hosting the next event on Wednesday, October 16th at The Alan Manchester. The focus of this event will be our new STRATOS partner programme.
Sign up
Exertis Enterprise Roadshow
Exertis Enterprise are hosting a UK Roadshow this month at Bowood Hotel Golf and Spa Resort. The Exertis Enterprise team and leading vendors will unveil the latest tech solutions and showcase Dragon's Den style presentations. There will also be spa and golf experiences for guests. This event is by invite only.
Find out more
Don't miss your chance to get involved in our new look PC+ enablement programme
Find out moreMeet our new partner

Drayton Wiser are a smart thermostat and heating control brand. They offer heating and cooling complete systems and create an energy saving eco system.
You can benefit from ordering Drayton Wiser smart thermostats and heating hub devices, including TRVs, smart control devices and smart home heating solutions.
Request a call backThe true impact of AI
Welcome to our Great Insights update. Our focus this month is on the transformative power of AI.

Tim Griffin, CEO of Exertis
"Everyone is talking about AI. While its short-term impact might be overestimated, its long-term potential is likely underestimated. To invest in AI, understanding use case models is crucial. We are still in the early stages of realising AI's full potential in various environments. AI will become as integral to our lives as the internet is today. Although the .com boom had a slow start, it eventually revolutionised everything, and AI will follow the same path."
Curious about our latest offering in AI technology?
Exertis Enterprise launches the
ground-breaking AI Pod

Exertis Enterprise, a leader in delivering cutting-edge technology solutions, have developed and announced the launch of the AI Pod, a pioneering solution designed to democratise AI and HPC technologies for businesses of all sizes.
Find out moreBuilt to enable a wide range of industry applications, offering unmatched performance, minimised latency, and enhanced software optimisation. This versatile and scalable platform provides organisations with a turnkey solution that includes comprehensive support and installation, ensuring a seamless integration into existing systems.

Simon Regan, AI Lead at Exertis Enterprise and the driving force behind the AI Pod, highlighted its market potential:
“The AI Pod is not just a product; it’s a catalyst for change. By breaking down the barriers to advanced AI and HPC solutions, we are making these technologies accessible to companies regardless of their size or sector. Our aim is to empower businesses to harness the full potential of AI to innovate and enhance their competitive edge.”

Tom Cox, Commercial Director at Exertis Enterprise, added:
“With the AI Pod, we are providing a platform for our customers to access the vast opportunity AI creates in the market today. Our role is to enable our customers and partners, working hard to remove complexity, and ensuring they have the right tools and support as they go to market"
We also offer:
Whitebox AI platforms
NVIDIA certified HGX
AI Centre of Excellence
Stock up on the latest
AI-enhanced devices

Samsung Galaxy Book4 Edge
This next-gen AI PC will change the way users work, create and play through the power of AI. Designed for enhanced portability and combining Galaxy AI with Microsoft Copilot AI assistant
Enquire now
Samsung Galaxy Book4 Pro
Powered by Galaxy AI, this device is built for professionals. Offering incredibly strong performance for all day-to-day tasks, boasting a 16” or 14” anti-reflective touchscreen display with a sleek and slim design.
Buy now
Lenovo ThinkPad L16 Gen 1
Powered by Intel® Core™ Ultra processors, the first generation of the 16" ThinkPad L16 laptop taps into AI-assisted productivity like never before.
Buy now
Lenovo ThinkPad T14 Gen 5 (14" Intel)
14” super thin, lightweight, & performance-focused business laptop. AI-assisted productivity fuelled by Intel® Core™ Ultra processors.
Buy nowWindows 10 support ends
on October 14th 2025..
That means customers only have 1 year to upgrade to Windows 11 with up-to-date functionality and better performance features, such as Microsoft Copilot.
We found the Microsoft Copilot integration into Microsoft 365 applications can increase business productivity, creativity and efficiency.
5 hours
per week saved on meeting note-taking

Save 6 hours
per PowerPoint presentation
Maximise Excel
without extensive training courses
Don't delay!
Shop Windows 11 devices todayThe AI age has landed


Offer your customers the chance to unlock AI potential for the modern workplace with secure, sustainable devices. Lenovo are leading the way, and we have stock of these powerful devices ready and waiting for your orders.
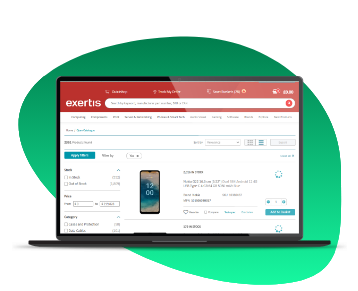
This year, we've focused on making our Online Store a one-stop shop for your needs. The team have been really busy making the site a smoother, safer and easier to navigate solution for our partners.
Have you tried out these new tools?
The key to safety
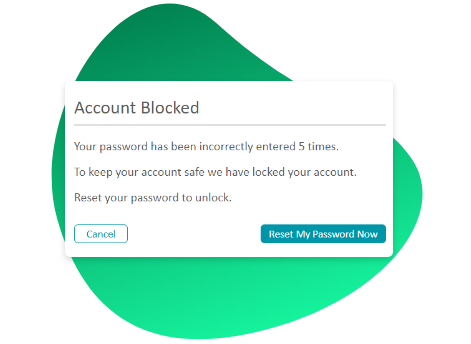
To protect your account and personal information, we’ve enhanced our security measures, including the introduction of one-time multi-factor authentication (MFA) for sensitive areas such as user information and account settings.

To protect your account and personal information, we’ve enhanced our security measures, including the introduction of one-time multi-factor authentication (MFA) for sensitive areas such as user information and account settings.
Find out about all the latest
Exertis Online Store updates
Explore now
Fill in the form below and someone will get back to you shortly
Don't miss out on any issue
Take a browse back through our previous Great Insights editions to stay in the know on what everyone is talking about.